Recent News
Lorem ipsum dolor sit amet, consectetur adipiscing elit. Ut efficitur condimentum mauris. Mauris in consequat mauris.
The Savvy Shopper’s Secret: Finding High-Spec Laptops in the Refurbished Market
"Learn how to identify and secure powerful, feature-rich laptops at a fraction of the cost." "Imagine walking into a high-end electronics store, eyeing the sleekest,...
Community Engagement is Mandatory for AI to Work in Under-Resourced Communities
Community Engagement and Needs Assessment: Example: Suppose we’re working with a low-income neighborhood facing health disparities. Steps: Organize community meetings...
Harnessing AI for Under-Resourced Communities: Solutions and Implementation Strategies for Non-Profits
#3 Welcome back to the third installment of our blog series on the transformative potential of Artificial Intelligence (AI) in underserved inner-city communities. In...
Implementing AI in Inner-City Communities: Detailed Insights and Strategies
#2 Implementing AI in Inner-City Communities: Detailed Insights and Strategies Introduction: As we continue our exploration of the pros and cons of artificial...
Pros and Cons of Artificial Intelligence in Under-Resourced Communities
#1 Pros and Cons of Artificial Intelligence in Under-Resourced Communities Introduction Artificial Intelligence (AI) is revolutionizing various sectors, from healthcare...
VPNs Simple and Safe
A VPN, or virtual private network, creates a virtual “tunnel” of encrypted data running over the public internet. VPNs first became popular as a way of connecting...
Why You Should Start Using A VPN
Why You Should Start Using a VPN September 28, 2019 | lmgtfy | VPNs And How to Choose the Best One for Your Needs You have heard the acronym; you may know what a...
The Importance of Strong Passwords
Keep your computer, data and accounts safe with strong passwords. Your first line of defense on the Web is creating the strongest password possible to protect your...
How To Create A Password You Can Remember
Five Methods:Using Phrases, Using Codes, Doubling It, The Bridge Shuffle, Upside-Down and Backwards Coming up with a password that is both safe and memorable gets...
KNC Jupiter Very First ASIC Bitcoin Miner
I am a Newbie to Crypto Currency. I'm also very lucky! Today, I had the good fortune to see one of the very first KNC Jupiter ASIC Bitcoin Miners! Let me tell you what...
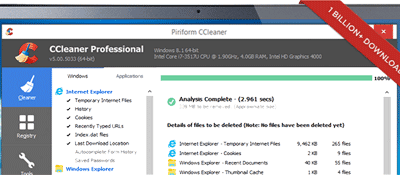
Keep Your Device Clean
Is your device running a bit slower than usual? Maybe random screens are popping up? Does your bank account have unknown charges on it? These are some signs that your...
Tor Project
Another tool to consider for your anonymity and protection online, is the Tor Project. Below is the beginning of information about the Tor Project. To see the complete...
Internet Security: College Bound!
As your son or daughter heads off to college, he or she is packing a smartphone, and undoubtedly one or more other devices such as a laptop or tablet that are essential...
Internet Security Tips For Students In Middle School And High School
Between the ages of 10 and 11 is, on average, when kids get their first cellphone. So by the time they reach junior high and high school, they likely know more about...
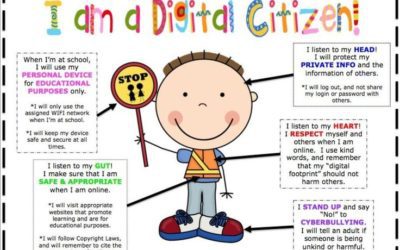
Internet Safety for Elementary School Students
With back-to-school preparations for clothing, backpacks and school supplies going on, keep in mind, with our world continuing to move online, it’s also a good time to...
Common Mobile Phone Scams & How to Avoid Them
As smartphone technology continues to evolve, it also paves the way for an increasing amount of mobile phone scams. These scams can cost their victims anywhere in the...
RACHEL PLUS CONTENT
Storyboard for RACHEL Plus Video-1 Today we’re going to look at some of what RACHEL is, connecting to RACHEL, and what content is available in RACHEL. First, let’s...
RACHEL-PLUS CONTENT-2
RACHEL-PLUS CONTENT-2 Storyboard for RACHEL Plus Content-2 1. RACHEL stands for Remote Access Community Hotspot for Education and Learning.2. All of RACHEL’s content is...
OffLine Education with RACHEL-Pi
Read More In the next few posts, I will share info about a learning tool I was introduced to. It is called RACHEL. RACHEL stands for Remote Access Community Hotspot for...
Secure Your Passwords
Secure your passwords Passwords are the first line of defense against cyber criminals. It’s crucial to pick strong passwords that are different for each of your...
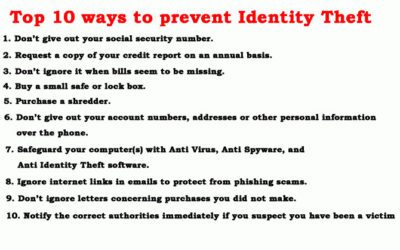
Prevent Identity Theft
Prevent Identity Theft Just like burglars and thieves, cyber criminals have many different ways to steal personal information and money. Just as you wouldn’t give a...
Logistics/Delivery
Attention!! Because one of our offices' proximity to the San Pedro Ports, we deliver electronic parts and accessories to several vendors in the South Bay. If you...